A web server is a software or hardware program that stores, processes and distributes web files (pages, text, images, etc.) to users as soon as they make a request.
Before a web page is displayed, it is a whole process that is performed by web servers. These are essential elements for the proper functioning of websites
And to better understand the importance of a web server, it is useful to address the following points:
- What is it?
- What are the most common web server software?
- How to ensure the security of your server?
It is around these various points that this article will be articulated.
Chapter 1: Web Server – What is it?
In this chapter, we will discuss more aspects of a web server to help you understand its usefulness and how it works
1.1 What is a web server?
The web server is in charge of broadcasting the content of websites. Its role is to display the various requests of users and the content it distributes can be static or dynamic.
When it comes to static content, it is sent to the user’s browser as it was hosted on the server without modification. However, when it comes to dynamic content, it can be updated and modified before being sent.
It should also be noted that the Web server is often an integral part of a set of programs designed to
- Sending and receiving e-mail;
- Requesting FTP (File Transfer Protocol) files
- Designing and distributing web pages.
1.2. how do web servers work?
The web server is accessible through the domain names of websites and delivers the content of the site to the user who requests it.
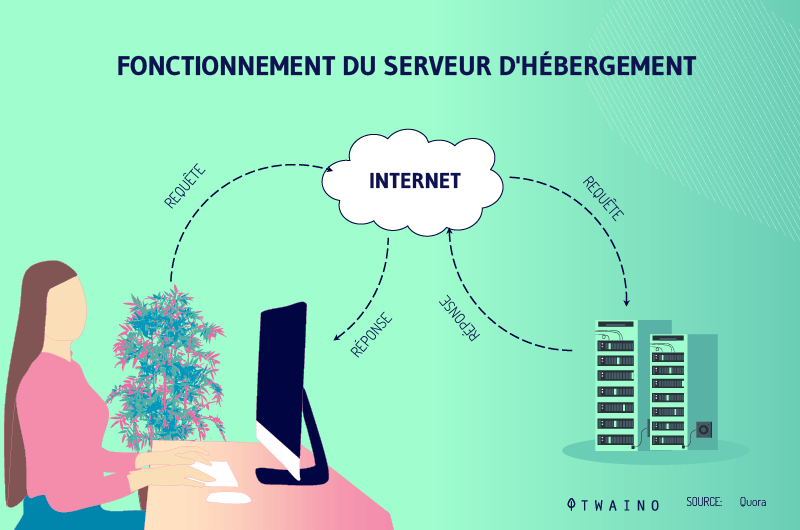
When a user requests a particular site or certain information from their browser, the browser will request the file via the HTTP protocol. This is a protocol designed to ensure communication between the client and the server on the web.
It is important to note that the current trend is to move to HTTPS (HyperText Transfer Protocol Secure). This is the secure version of HTTP.
HTTPS is the use of HTTP coupled with a security layer. This not only encrypts all data exchanged between the client and the server, but also confirms the identity of your website.
Once the web server receives the request, the HTTPS protocol will accept the request. It then takes care of finding the content among the different files that are hosted in the server
As soon as it finds the content, it takes care of sending it to the browser via HTTPS.
More precisely, the process is as follows:
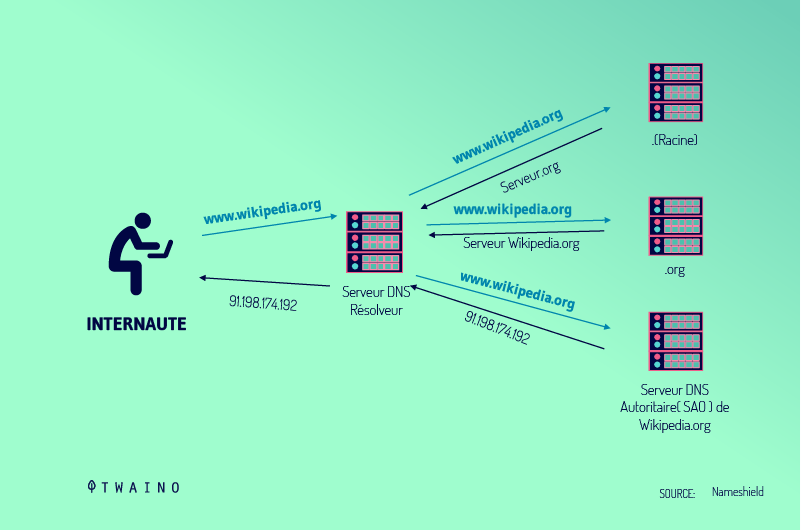
- A person called a “client” or “user” types a URL into the address bar of their browser (Chrome, Firefox, etc.).
- The web browser obtains the IP address of the requested domain name either by translating the URL via DNS (Domain Name System) or by searching its cache. This will take it to a web server.
- The browser will then request the specific file from the web server with an HTTPS request.
- The web server responds by sending the requested page to the browser, again via HTTPS. An error message is sent by the server if the page does not exist or if there is a problem
1.3. The different error messages that a web server can send
In case of problem, the server can send different error messages. Here are the most common messages and their causes.
1.3.1. Client error code
When it is an error that comes from the client, the server sends an error message with three digits that begins with 4.
- 400 Bad Request
The server sends this error code when it does not understand the request made by the client.
Source ubuntu-mate
It often appears when the client sends the request from an insecure operating system. Also, it can occur when the internet connection is unstable or when the browser has problems.
To stop this error, it is advisable to open the page in question in another browser. However, it is advisable to check for security updates and clear the cache first.
- 403 Forbidden
When this message appears, it means that you are not allowed to access the requested content. Thus, the server refuses to give it to you. This error occurs when browsing is prohibited for a given site, file or directory.
Source community.shopify
To solve this error, you must first check the name and extension you requested
Once everything is in order, you can try again. If the problem persists, clear your cache and try again.
- 404 Not Found
This error message is very common:
It simply means that the web server is unable to find the information requested by the browser user. This often happens when the requested file is already deleted
To solve this problem, you should check whether the URL was entered correctly and whether the information in question is still available
1.3.2. Server error code
When it is an error that comes from the server itself, it sends a three-digit error message that starts with 5.
- 500 Internal Server Error
This type of message often appears when the server, for unforeseen problems, is unable to respond to the client’s request.

Source howtogeek
The 500 error is often due to:
- A problem while installing or updating your software;
- A conflict between a new plugin and other plugins.
To solve this problem, you need to check your logs. It is very likely that you will see the reasons for the error there.
This type of error is encountered when the server is unable to read HTTP requests.
Source wpkube
Less frequent than the others, it often appears when the server is overloaded or under maintenance.
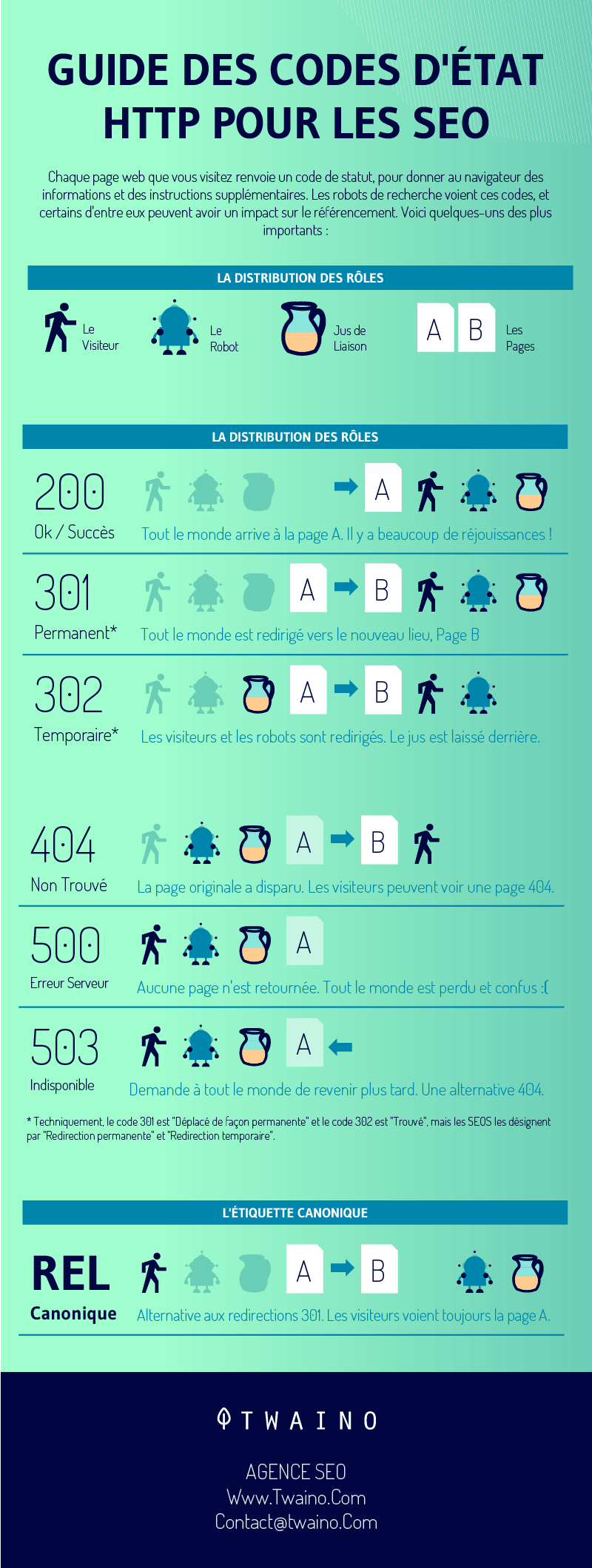
Here is a summary of the different status codes and their impact on your SEO
Let’s move on to web server software:
Chapter 2: What is web server software?
In this chapter, I give you information about web server software, some examples, and tips for choosing what’s right for you.
2.1. Web server software: Definition
Web servers are often computers that store the files necessary for the proper functioning of the site. The web server software are only programs installed and executed on the physical server
They are applications that can access the files saved on the physical server in order to use them for different purposes. They play an intermediary role between the server and the client’s browser
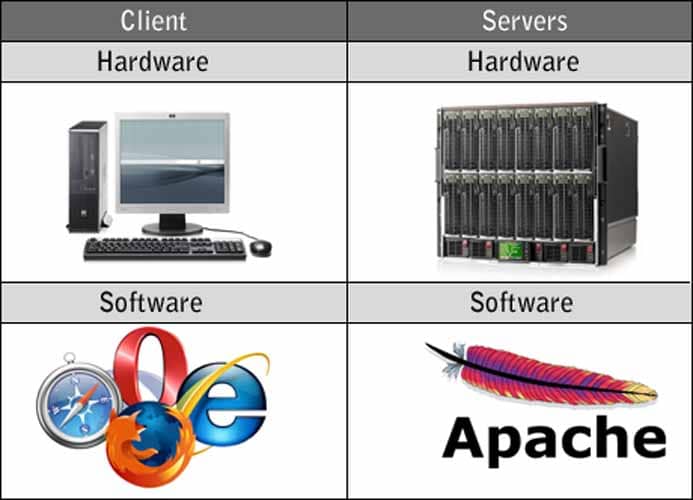
Source Webdevelopersnotes
When a visitor to your site wants to load a given page, his browser sends the request to your server. It is up to the web server software to send the response to the client’s browser with all the required files.
In fact, the web server software is responsible for retrieving the content requested by the client from the main server and sending it to the web browser
The biggest challenge of web server software is to serve several web users at once, each requesting different pages
Web server software includes modules for
- Security
- Caching
- URL rewriting
- Password authentication, etc
You have the possibility to configure your own software.
2.2. examples of web server software
There are a number of web servers available, some including:
This server was designed by the Apache Software Foundation.
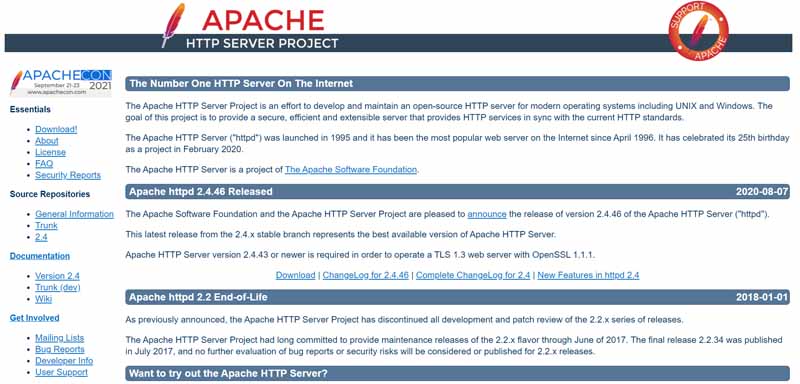
Perfectly suited for most operating systems, it is a free and open source web server. To use it, you need to have the Apache license.
Created by the large company Microsoft, this server can be used for Microsoft platforms. Unlike Apache, this web server is not open source.
This is one of the best known open source web servers. It is a very scalable software that uses low resources
Nginx is able to handle multiple sessions simultaneously. It has a special architecture and can be used as a proxy server as well as a load balancer.
This is a web server that comes with the FreeBSD operating system.
Lighttpd is a fast and free server that provides some security. It should also be noted that it consumes less CPU power than the others.
This is a free web server developed by Sun Microsystems. It is capable of running on Windows, Linux and Unix. It can efficiently manage medium to large websites.
2.3. how to choose your web server software ?
To choose your web server, you must take into account many parameters that can influence the daily operation of your site.
These are the following criteria:
- The security of your data the web server software you choose must offer guarantees regarding the security of your data
- The compatibility of the server with the operating system the web server must be compatible with your operating system. You must analyze which web server would work best with your choice of operating system
This is because the Microsoft IIS web server can only be run on a Windows operating system, for example, while a web server such as Apache could run on several different operating systems
- Support for site-building software it is also important to ensure that the web server supports the web authoring software you are going to install
If you plan to use Java-Server pages, you will probably need to choose Apache Tomcat or similar software
- Managing web applications for PHP-based web applications, several options are available. But if you want to run a web application based on ASP.NET, you will certainly need Windows.
- The budget budget: Large web servers like Apache and IIS have their own server operating systems. However, others may have their own additional cost. It is important to consider your budget
These are some criteria you can consider when choosing server software. That said, note that as someone who simply wants to create your website, you don’t need to consider them.
Indeed, the hosting services already do this and it is up to you to simply choose one of the packages they will offer you according to your needs.
Chapter 3: How to ensure the security of the web server?
Given the importance of the web server for the proper functioning of the sites, it is important to ensure its security
Indeed, the latter can be threatened in several ways. You will then have to find solutions to protect your data in case such an incident occurs.
3.1. The different types of attacks on a server
There are several types of attacks that malicious people can use against your server.
3.1.1. DOS attack
A hacker can provoke a denial of service attack by sending numerous service request packets in order to impact the service capacity of the web server.
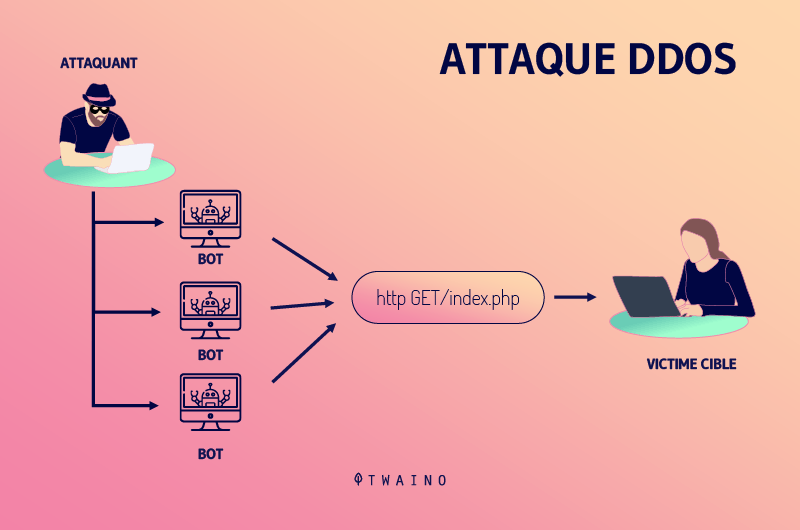
He can also try to exploit a programming error in the application causing a DOS attack
This could be an attack by:
- Buffer overflow
- SYN Flooding
- HTTP get Request Flooding
- Ping of Death.
3.1.2. SQL injection attacks
They are used to degrade the website. When a hacker discovers that the input fields are not properly cleaned, he can add SQL strings to maliciously create a query that is executed by the web browser.
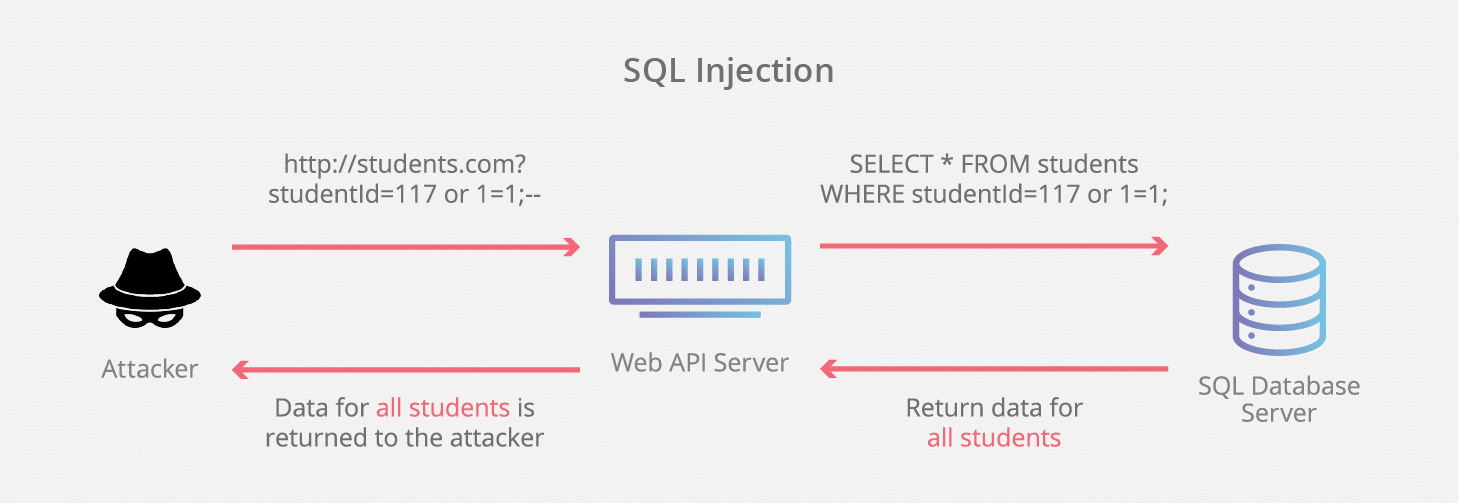
Source towardsdatascience
It can store malicious or /irrelevant data in the database. Thus, when the website is requested, it will display inconsistent data. The consequence is that the website is damaged.
3.1.3. Directory traversal and misconfiguration attacks
Directory traversal is a vulnerability where a malicious person can access beyond the web root directory from the application
If he is able to access beyond the web root directory, he can execute operating system commands and obtain sensitive information or access restricted directories.
There are also misconfiguration attacks. If unnecessary services are enabled or default configuration files are used, detailed/error information is not hidden.
A hacker can compromise the web server via various attacks such as password cracking, error-based SQL injection, command injection, etc.
3.1.4. Phishing attack
A hacker can redirect the victim to malicious websites by sending an email link that looks authentic. Unfortunately, this link redirects them to another web page whose purpose is to steal their personal data.

Source titanhq
These are some of the different attacks, but note that there are other types of web server attacks.
These include
- Parameter tampering
- Cookie tampering
- Invalid input
- SQL injection
- Buffer overflow attacks.
3.2 Methodology to recover an attacked server
3.2.1. Information gathering and vulnerability analysis
Initially, to learn more about the origin of the attack, information about the server in question must be collected from various sources such as
- Sites
- WHOIS ;
- Netcraft ;
- Nmap ;
- Httrack
- Etc
This different information collected will be used to analyze the web server and the applications running on it. To do this, it will be necessary to use certain automated tools such as:
- Nessus
- OpenVAS
- Tripwire IP360
- Comodo Hacker Proof
- Vulnerability Manager Plus ;
- Wireshark
- Retina Network Security Scanner;
- And more.
The results may show various threats and vulnerabilities on the target web server. These vulnerabilities can be resolved later using tools or manually
As an example of tools to resolve the issues, we can mention
3.2.2. Adopting countermeasures
Once you identify the threat, you can adopt the following countermeasures:
- Update and patch web servers regularly;
- Ensure secure storage of files related to server configuration;
- Scan all vulnerabilities in applications running on the web server;
- Use IDS and firewalls with updated signatures;
- Block all unnecessary protocols and services;
- Use secure protocols;
- Disable default accounts, follow a strict access control policy;
- Install antivirus software and update it regularly;
- All operating systems and software used should be the latest and updated.
However, you should not wait until you are under attack before adopting the above measures. They should be part of your daily routine to prevent attacks.
In summary
The web server is an important software or hardware for the distribution of content on a website. It also allows to host one or more sites. Thanks to software, it allows the client to have the files he requests
There are several types of servers and it is important to take into account certain criteria to choose the one that suits you best. On the other hand, malicious individuals can attack your web server
To avoid this, it is advisable to adopt daily preventive measures. But when attacks do occur, use the alternatives listed in the article to stop them.
I hope this content was useful to you, if so please let us know in comment.
Thanks and see you soon!