HTTP stands for Hypertext Transfer Protocol . It is essentially a communication protocol used to conduct information between the client and a web server.
The HTTP protocol was created alongside HTML to build the first interactive text-based web browser known as the original World Wide Web. This innovation marked the beginning of modern internet navigation.
Today, HTTP remains one of the core technologies of the internet. Every online action, whether loading a website, submitting a form, or accessing multimedia content, relies heavily on HTTP communication.If you are an internet user, understanding what is HTTP and how it works is essential. This guide explains everything you need to know about the protocol, from its history to its technical operation and primary purpose.
Chapter 1: What Does the HTTP Protocol Mean?
Because the HTTP protocol is one of the fundamental components of the internet, this chapter explores the essential concepts needed to understand its definition, evolution, and functioning.
1.1 Definition and History of HTTP
The HTTP protocol is a standardized method used for encoding and transmitting information between a web browser and a web server. It is considered the primary protocol responsible for delivering web content worldwide.
The earliest version, HTTP 0.9, appeared in the late 1980s but offered limited functionality. Despite its simplicity, it laid the groundwork for modern web communication.
Combined with HTML and URLs, HTTP became the foundation of the global information initiative known as the World Wide Web (WWW). This groundbreaking innovation was led by Tim Berners-Lee at CERN in Geneva, initially designed to facilitate information sharing among physicists.
Due to the limitations of HTTP 0.9, Berners-Lee introduced improvements that resulted in HTTP/1.0, the first complete version of the protocol in 1991. Later, it was submitted as RFC 1945 to the Internet Engineering Task Force (IETF) in 1996.
The growing popularity of the graphical browser NCSA Mosaic accelerated web adoption. However, certain weaknesses in HTTP/1.0 became evident, including:
- Inability to host multiple websites on a single server (virtual hosting limitation)
- Lack of connection reuse
- Weak security mechanisms
Other performance constraints
These challenges led to the development of HTTP/1.1, introduced as RFC 2068 in 1997 and updated in 1999 under RFC 2616. This version significantly improved efficiency and scalability, shaping modern web communication.
1.1.2 How the HTTP Protocol Works2.
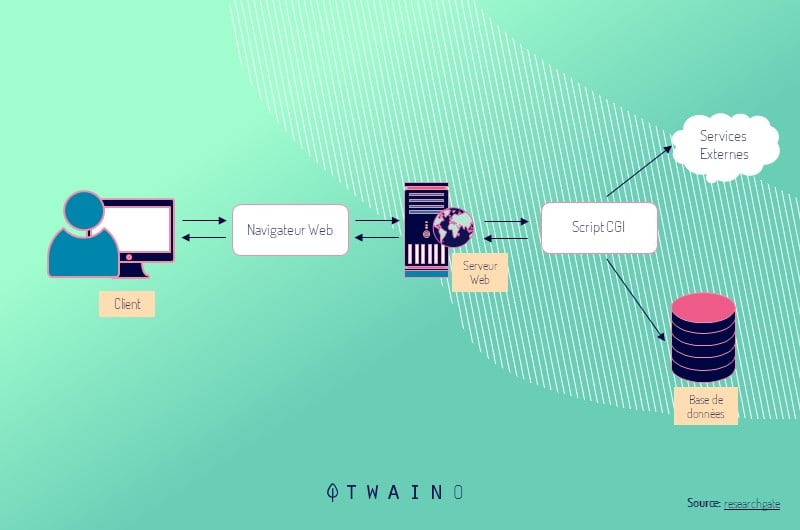
Whenever a user performs an action online, they unknowingly rely on the HTTP protocol. It is responsible for sending requests from the client to the server and returning responses containing requested data.
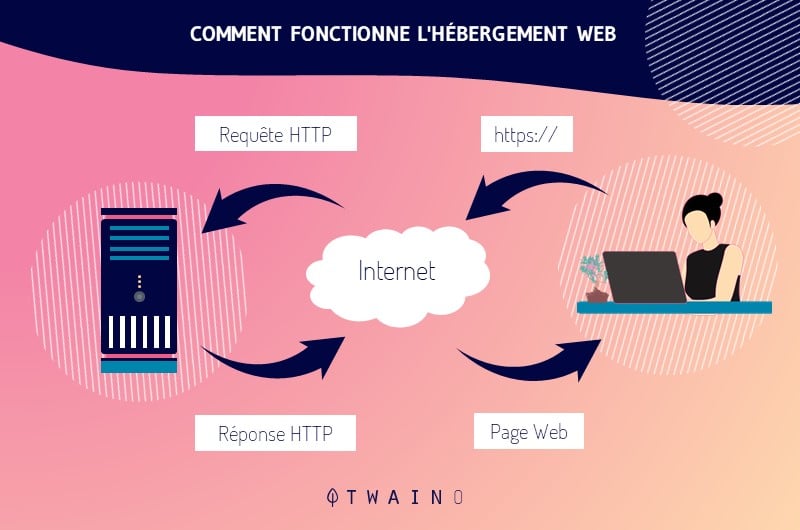
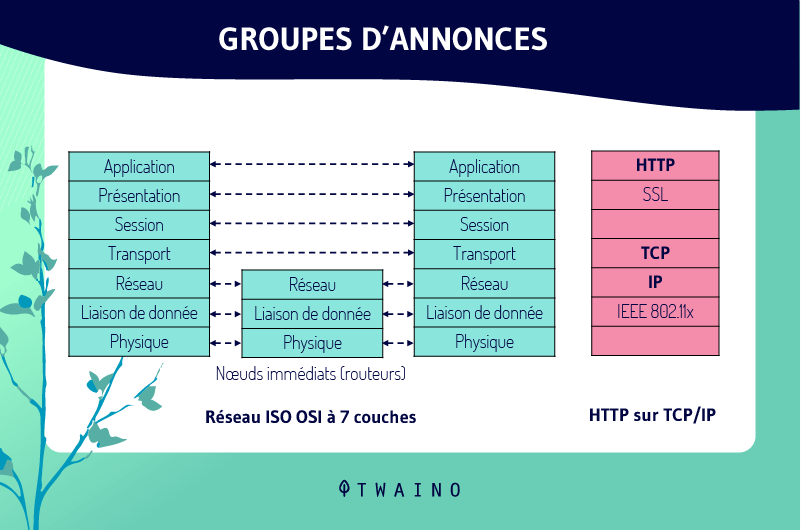
This process requires HTTP to operate at the application layer on both the client and server sides. Without this shared protocol, communication cannot occur.
The client request is typically executed through a web browser, which manages the entire exchange and displays the requested resources on the user’s screen. Browsers interpret web pages as collections of interconnected objects linked by hyperlinks.
Therefore, a typical web page consists of:
- An HTML document
- Scripts
- Images
- Multimedia elements
- Other external resources
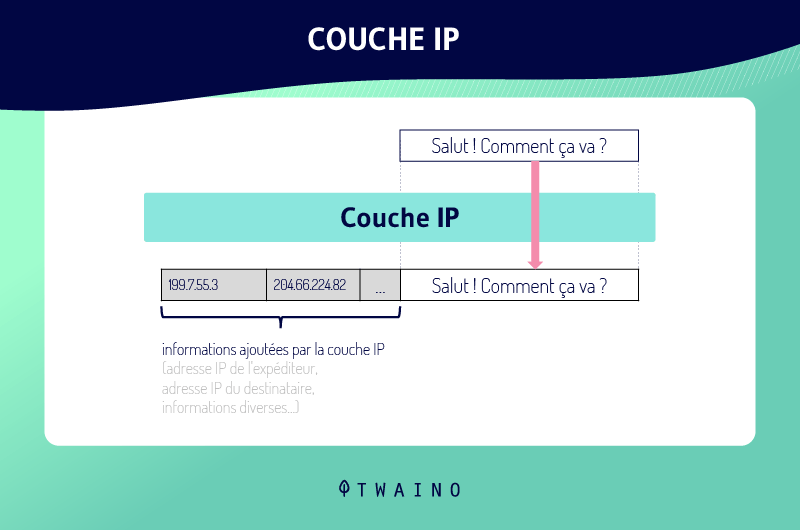
The HTTP protocol relies on TCP at the transport layer to ensure reliable data transmission. This relationship is often described as HTTP vs TCP, where HTTP handles application-level communication while TCP guarantees delivery accuracy.
The main reason HTTP uses TCP instead of UDP is reliability. TCP ensures that all transmitted data arrives intact and in order. However, this reliability introduces latency because TCP must first establish a connection through a process known as the TCP handshake.
Reliable transfer is essential for HTTP. If parts of an HTML page fail to reach the browser due to transmission errors, the webpage may not render correctly or may appear corrupted.
Although HTTP belongs to the application layer and TCP to the transport layer, they interact through sockets. A socket acts as the interface point between these layers.
For example:
- When a user requests a web page while sending an email, two sockets are created:
- One managing HTTP communication
- One managing HTTP communication
Another handling email protocol communication
However, when opening two web pages simultaneously, a single socket may be used because it corresponds to one process. The socket manages incoming packets independently, enabling separate rendering of requested pages.
1.3 The Purpose of the HTTP Protocol
When discussing HTTP purpose, the protocol’s main role is facilitating the transfer of website data across the internet.Hypertext refers to the standard web format where pages link to one another via clickable hyperlinks. The HTTP protocol provides a standardized mechanism for browsers and servers to exchange this information.
Although websites are primarily built using HTML, HTTP is now used to transfer a wide range of content, including:
- CSS files
- Images
- Audio files
- Video content
- API responses
- Downloadable resources
Computers connect to web servers using HTTP to request files at specific web addresses. When retrieving data, browsers typically send an HTTP request GET message. When submitting forms or uploading files, they use HTTP POST or HTTP PUT requests.
You can observe these HTTP requests using built-in developer tools available in most browsers.
Today, HTTP is used far beyond browsers. Many applications rely on it to communicate with servers, making it a universal web communication protocol.
Developers choose HTTP because it is widely understood and supported across platforms. Another advantage is that HTTP traffic is generally allowed through network firewalls designed to permit web traffic, enabling seamless communication across home and enterprise networks.
1.4 Advantages of the HTTP Protocol
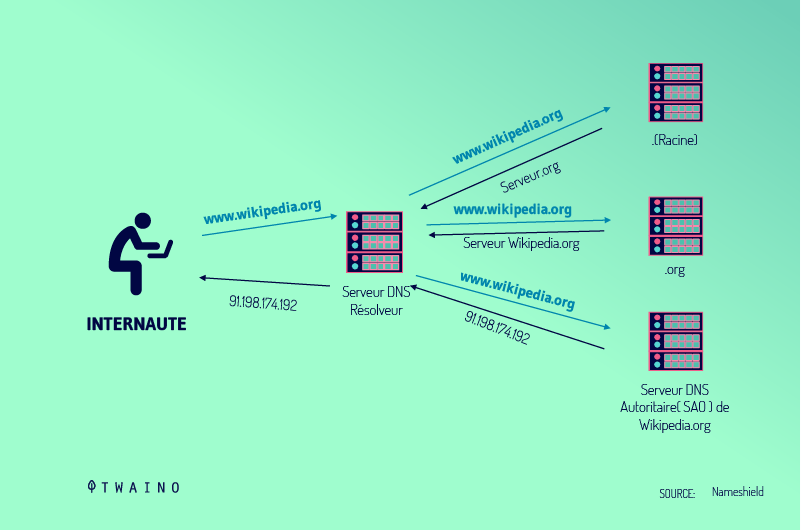
One of the first things you should know is that the HTTP protocol uses an advanced addressing scheme. It associates IP addresses with recognizable domain names, making resources easier to locate across the World Wide Web.
Compared to traditional numeric IP addressing, this approach simplifies user interaction with the internet and improves accessibility. This is one of the key HTTP advantages that contributed to the rapid adoption of web technologies.
Another benefit is extensibility. Whenever an application requires additional capabilities, HTTP can support them through extensions, plugins, or additional modules that enable the display of relevant data and enhanced functionality.
With HTTP, each file is transferred through an independent connection that closes after completion. Because of this mechanism, only one element of a webpage is transmitted at a time, which reduces the likelihood of interception during transmission.
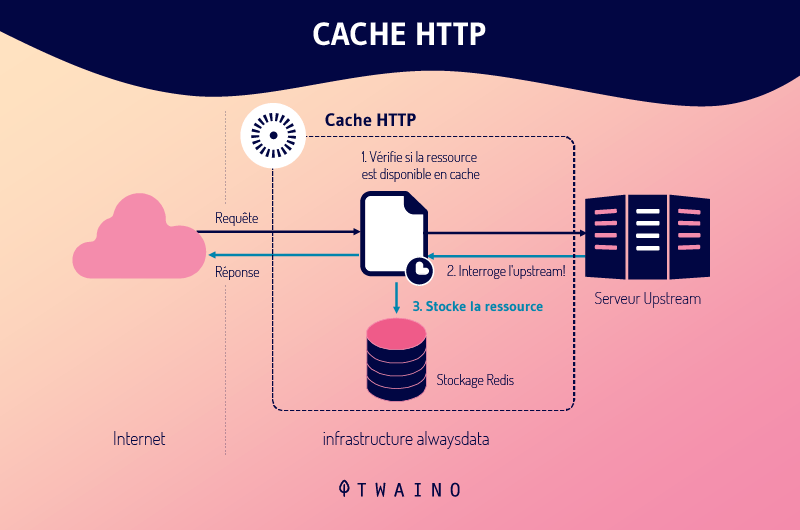
Additionally, HTTP supports caching. When a webpage is loaded for the first time, its resources are stored in internet caches known as page cache. As a result, revisiting the page allows faster loading times since previously downloaded resources can be reused instead of fetched again from the server.
These features collectively demonstrate why HTTP remains a foundational web communication protocol despite the emergence of more secure alternatives.
1.5 Disadvantages of the HTTP Protocol
Despite its widespread adoption, HTTP presents notable limitations, particularly in terms of HTTP security.Because HTTP does not rely on data encryption, transmitted content can potentially be modified by malicious actors. This lack of encryption makes HTTP a non-secure protocol, exposing data to interception and manipulation.
Privacy is another significant concern. If a hacker intercepts an HTTP request, they may access all webpage content, including sensitive information such as usernames, passwords, or personal data.
Furthermore, even after receiving all required data, HTTP clients may not immediately close connections, creating temporary communication gaps where the server may be unavailable. This behavior can lead to inefficiencies and resource wastage.
Another drawback is connection overhead. When HTTP must establish multiple connections to load a webpage, administrative overhead increases, affecting performance and server workload.These HTTP disadvantages ultimately led to the development of HTTPS, a secure version of the protocol designed to address security vulnerabilities.
1.6 What Is the Difference Between HTTP and HTTPS?
While HTTP stands for Hypertext Transfer Protocol, HTTPS refers to Hypertext Transfer Protocol Secure.
You may notice that some URLs begin with HTTP while others start with HTTPS. The additional “S” indicates secure encryption, ensured through an SSL certificate.
HTTPS uses public key cryptography where encrypted data is decrypted by the recipient using a corresponding private key. This public key is provided within an SSL certificate.
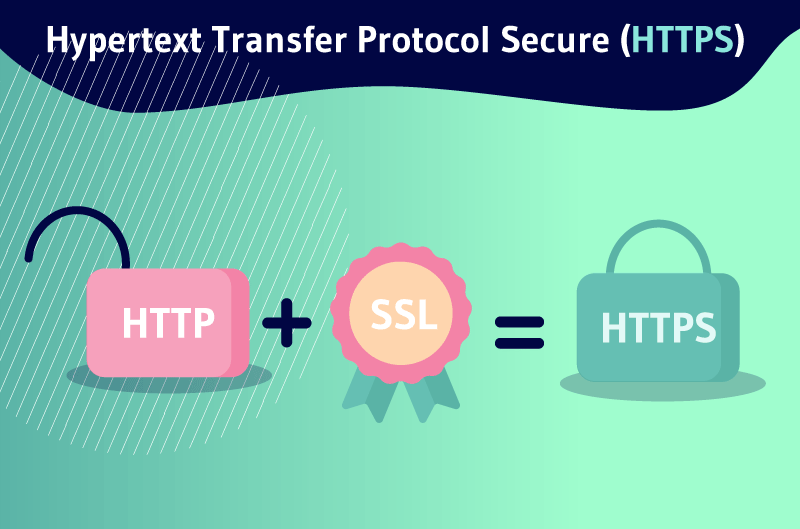
An SSL certificate acts as a digital identity card verifying that a website is authentic and protected against external threats. Websites that collect sensitive user information such as personal addresses or credit card numbers are required to obtain SSL certification.
The HTTPS encryption mechanism provides several advantages:
- Protection against hackers: Encryption safeguards sensitive data from interception and identity theft.
- Authenticity and trust: Users prefer interacting with secure websites and are less likely to transact on unverified platforms.
- Higher conversion rates: Studies indicate that secure e-commerce websites may experience conversion increases ranging from 18% to 87%.
In contrast, HTTP simply transmits messages without encryption, leaving data highly vulnerable to cyberattacks. This distinction explains the growing importance of HTTPS in modern web security strategies.
Chapter 2: What Is an HTTP Status Code?
When a client sends requests to a server, the server responds with HTTP status codes alongside message payloads. These codes are crucial because they indicate how the client should interpret the server’s response.
The HTTP specification defines numeric ranges corresponding to different response categories.
1xx: Informational Messages
This class represents provisional responses. All HTTP/1.1 clients must accept the Transfer-Encoding header.
The server may send an Expect: 100-continue message instructing the client to proceed with sending the remaining request data or ignore the message if already transmitted. HTTP/1.0 clients typically ignore this header.
2xx: Successful Responses
This category indicates that the client’s request was successfully processed. The most common code is 200 OK, meaning the server returned the requested data.
Other notable codes include:
- 202 Accepted: The request has been accepted but may not yet include the resource in the response. This is useful for asynchronous processing.
- 205 Reset Content: Instructs the client to reset the document view.
- 206 Partial Content: Indicates that only part of the content is returned, often with headers specifying range and expiration details.
These responses demonstrate successful HTTP request processing.
3xx: Redirection Responses
Redirection codes inform clients that requested resources have moved.
Examples include:
- 303 See Other: The resource is temporarily located at another URL.
- 304 Not Modified: Indicates that the resource has not changed and the client should use its cached version. This relies on ETag values, which are content hashes compared between client and server.
Redirection improves caching efficiency and bandwidth usage.
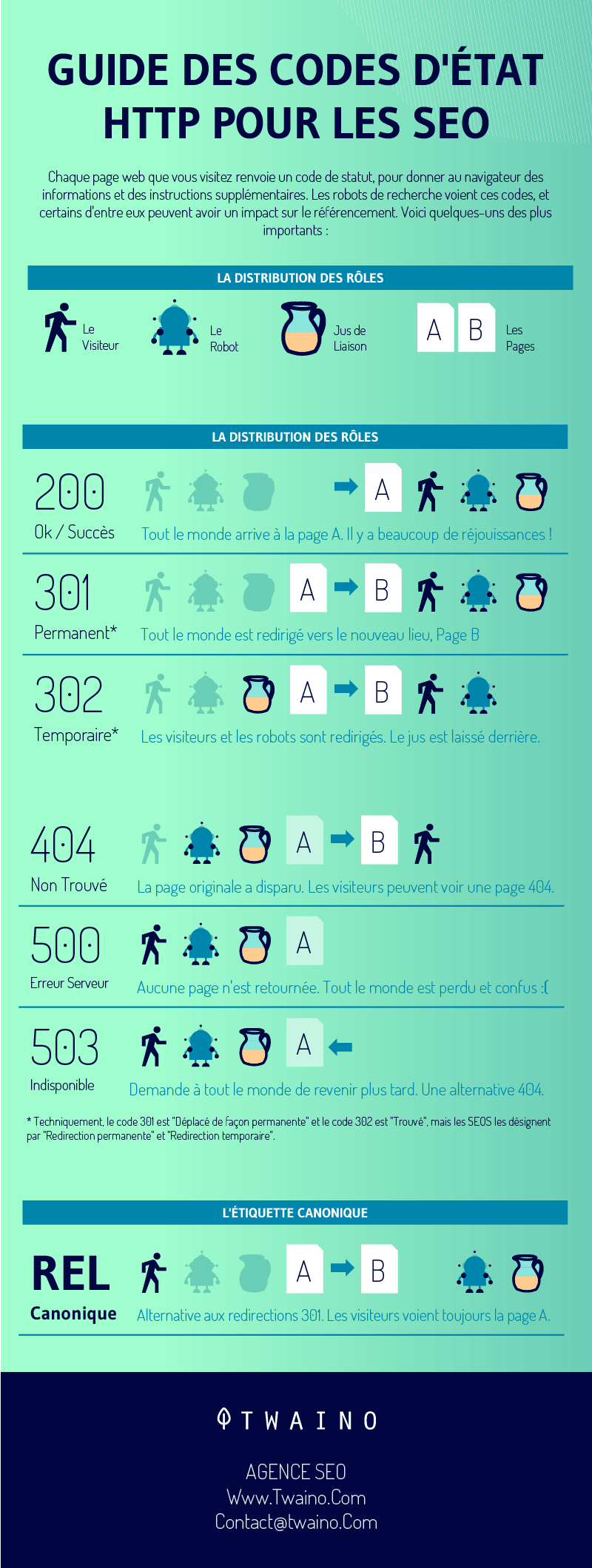
4xx: Client Error Responses
These HTTP error codes occur when the server determines that the client request is incorrect.
The most recognized code is 404 Not Found, indicating that the requested resource does not exist on the server.
Other common client errors include:
- 400 Bad Request: The request was malformed.
- 403 Forbidden: Access to the resource is denied.
- 405 Method Not Allowed: Invalid HTTP method used or unsupported by the server.
- 409 Conflict: The request conflicts with the current state of the resource, often seen in collaborative editing scenarios involving PUT requests.
Client errors typically require corrective action from the user or application.
5xx: Server Error Responses
This category indicates failures during server processing.
The most common code is 500 Internal Server Error, representing a general server malfunction.
Other examples include:
- 501 Not Implemented: The server does not support the requested functionality.
- 503 Service Unavailable: Occurs when the server is overloaded or an internal system failure prevents processing. Requests may time out without response.
These codes highlight issues within server infrastructure rather than client requests.
Conclusion
Since its earliest version, the HTTP protocol has remained the primary mechanism for data transmission across the internet. Every online interaction relies on HTTP to obtain responses from servers.
Understanding what is HTTP, its advantages, disadvantages, and role in modern web communication is essential for anyone using the internet or working in web development.
In this guide, we explored key aspects of HTTP, including its history, functionality, purpose, comparison with HTTPS, and interpretation of HTTP status codes.
I hope this article helped clarify complex concepts related to the HTTP protocol. Feel free to leave a comment if you have any questions or need further clarification.